Rack Cabling, Labeling, and Rack Design Standards
- Posted by
- Posted on May 25, 2026
- Audio / Video,Computers,IT Support,Networking,Router,Servers,Switch
- No Comments.
A clean rack is not just about appearance. Proper rack layout, cable management, labeling, power design, and thermal planning directly affect system reliability, serviceability, troubleshooting speed, and long-term support. Whether you are building a conference room rack, broadcast support rack, classroom AV system, control room rack, or equipment enclosure, the goal is the same: every […]
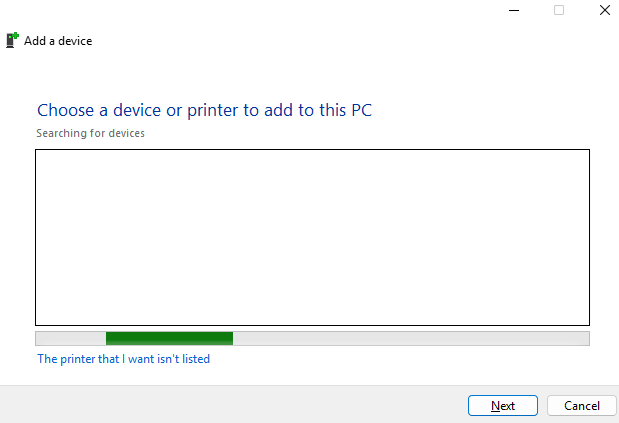
Run the Printer Installation UI as Administrator in Windows
- Posted by
- Posted on May 15, 2026
- Computers,IT Support,Windows
- No Comments.
In some situations, Windows may require administrator permissions to install or configure a printer. This can happen when adding a local printer, installing printer drivers, or modifying printer settings that require elevated rights. One way to launch the printer installation interface with administrator permissions is to open an elevated Command Prompt and run the Windows […]
Change the Maximum Size Limit for Outlook PST and OST Files
- Posted by
- Posted on May 15, 2026
- Computers,IT Support,Windows
- No Comments.
Microsoft Outlook stores mailbox data in PST and OST files. By default, modern versions of Outlook typically have a file size limit of 50 GB for Unicode PST and OST files. If Outlook reaches this limit, users may see errors stating that the Outlook data file has reached its maximum size. Microsoft provides registry values […]
So You Want to Be a Hacker, Eh?
- Posted by
- Posted on May 10, 2026
- Computers,Hacking,Lab,Linux,Mac OS,Microsoft Applications,Networking,Router,Servers,Switch,Video Conferencing,Virtualization,Website,Windows
- No Comments.
Let’s get one thing out of the way first. No, this is not about breaking into your school’s grading system, guessing your friend’s Instagram password, or “testing” your neighbor’s WiFi. This is about ethical hacking, also known as cybersecurity, where people are actually paid to find problems before the black hats (Malicious or Illegal hackers) […]
New Chrome Setting Which Blocks Local Network Access for Web Apps
- Posted by
- Posted on February 9, 2026
- Computers,IT Support,Mac OS,Windows
- No Comments.
Fixing Chrome and Edge Local Network Access Breaks Chromium-based browsers (Chrome, Microsoft Edge, Brave, Vivaldi, Opera) have introduced a Local Network Access permission model that can block or prompt when a website tries to reach local IPs (private ranges like 192.168.x.x, 10.x.x.x, 172.16-31.x.x, and sometimes loopback). In real-world support, this can falsely stop internal web […]
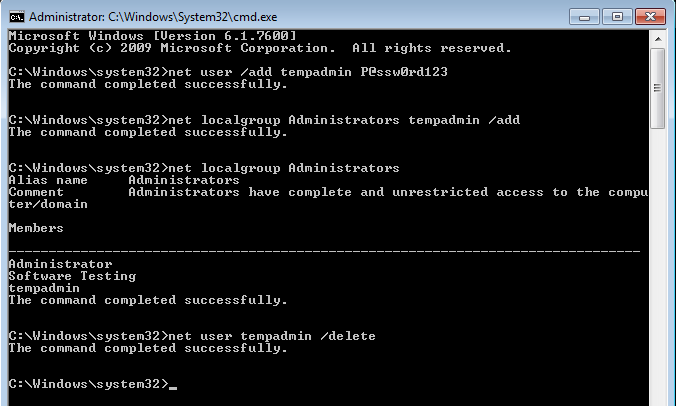
Creating and Removing Local Administrator Accounts in Windows
- Posted by
- Posted on February 9, 2026
- Computers,IT Support,Windows
- No Comments.
Local administrator accounts play a critical role in Windows system administration. They are commonly used for initial device setup, offline troubleshooting, break-glass access, or environments where domain connectivity is unavailable. This article walks through how to create, assign, and remove local administrator accounts on Windows computers using built-in command-line tools. These commands work on Windows […]
Apple Mobile Device Drivers on Windows
- Posted by
- Posted on February 8, 2026
- Computers,IT Support,Mac OS,Windows
- No Comments.
Understanding Apple Mobile Device Drivers on Windows If you support Windows systems in an enterprise or helpdesk environment, you have almost certainly run into issues where an iPhone or iPad simply refuses to appear when connected by USB. The device charges, but it does not show up in File Explorer, iTunes, or management tools. […]
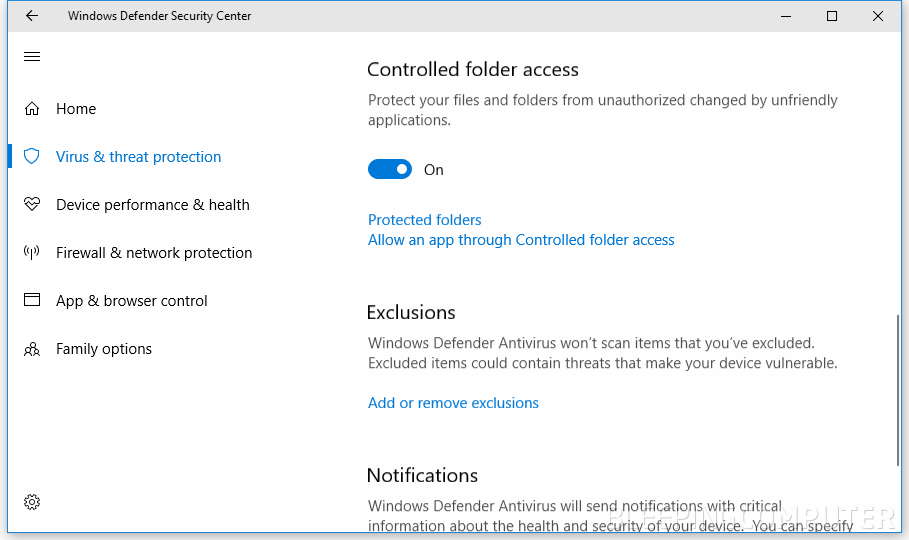
Controlled Folder Access
- Posted by
- Posted on February 8, 2026
- Computers,IT Support,Windows
- No Comments.
Windows Controlled Folder Access: How It Works, What It Does, and How to Turn It On or Off Controlled Folder Access (CFA) is a Windows security feature in Microsoft Defender designed to help stop ransomware and other untrusted apps from changing files in important folders. If you support Windows endpoints (or you are building a […]
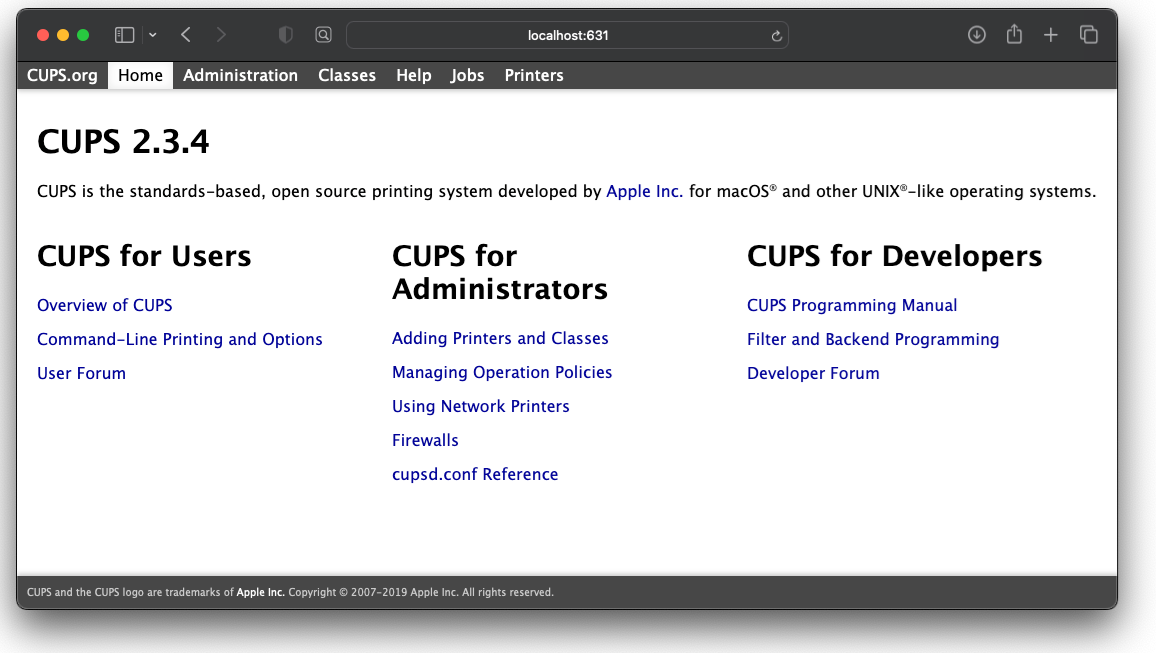
Mac CUPS: The Local Host Printing Interface Explained
- Posted by
- Posted on January 26, 2026
- Uncategorised
- No Comments.
CUPS (Common UNIX Printing System) is the underlying printing subsystem used by macOS to manage printers, print queues, and print jobs. It has been part of macOS since Mac OS X 10.2 and continues to serve as the core printing framework that applications rely on to communicate with both local and network printers. What Is […]
Outlook Email Calendar Permissions
- Posted by
- Posted on January 25, 2026
- Computers,IT Support,Microsoft Applications,Windows
- No Comments.
Outlook calendar permissions control how other users can see or interact with a mailbox owner’s calendar. These permissions are critical in Microsoft 365 environments where scheduling visibility, executive support, shared resources, and delegated access are part of daily operations. While the permission levels themselves are consistent, the way permissions are assigned depends on the platform […]
Recent Posts
- Rack Cabling, Labeling, and Rack Design Standards
- Run the Printer Installation UI as Administrator in Windows
- Change the Maximum Size Limit for Outlook PST and OST Files
- So You Want to Be a Hacker, Eh?
- New Chrome Setting Which Blocks Local Network Access for Web Apps
Archives
- May 2026
- February 2026
- January 2026
- December 2025
- October 2025
- September 2025
- August 2025
- July 2025
- June 2025
- February 2025
- January 2025
- July 2022
- February 2022
- January 2021
- July 2020
- May 2020
- February 2020
- December 2019
- August 2019
- January 2019
- July 2018
Categories
- Audio / Video
- Computers
- Hacking
- IT Support
- Lab
- Linux
- Mac OS
- Management
- Microsoft Applications
- Networking
- Printer
- Router
- Servers
- Switch
- Uncategorised
- Video Conferencing
- Virtualization
- Website
- Windows